With the increasing popularity of Spring Boot, it is essential to know how to add security features to your project. This blog post will show you how to do just that. We will walk you through the basics of setting up security in a Spring Boot application and give you some tips on making your project more secure. Besides this, this post blog post will help you ace the Spring boot interview questions and answers round easily.
Let’s get started!
What Is Spring Boot Security?

Spring Boot Security is a module that provides security features for Spring-based applications. It builds on top of Spring Security, which provides comprehensive security capabilities for Java applications. Springboot security offers several features that make it easy to secure a Spring-based application. In addition, it supports authentication and authorization and can be easily integrated with any Spring-based application.
How To Implement Security In Spring Boot Project?
There are a few ways to implement security in the Spring Boot project:
1. Use Spring Security
Spring Security is a powerful and popular framework for implementing security in Java applications. It can be used to secure resources, including web applications, RESTful APIs, and more. Here are the steps you can try:
- Add the Spring Security dependency to your project:
<dependency>
<groupId>org.springframework.security</groupId>
<artifactId>spring-security-core</artifactId>
</dependency>- Configure Spring Security:
You’ll need to configure Spring Security to protect your resources. You can do this by creating a security configuration file or by using annotations.
2. Use A Security Plugin
Several plugins can be used to add security to a Spring Boot project. Some popular options include the Spring Security Plugin and the Apache Shiro Plugin.
To use a security plugin in a Spring Boot project, you’ll need to add the appropriate plugin dependency to your project. Let’s understand more through the Spring Boot security example. Suppose you want to use the Spring Security Plugin, then you would add the following dependency:
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-security</artifactId> </dependency>Once you’ve added the plugin dependency, you can configure it by setting up a security configuration file or annotating. You can then secure your resources by using the appropriate security annotations or configuration options.
3. Use A Third-Party Security Solution
Some third-party security solutions can be used to add security to a Spring Boot project. Some popular options include Auth0, Okta, and Azure Active Directory.
To use a third-party security solution in a Spring Boot project, you’ll need to create an account with the provider and add the appropriate dependency to your project. For example, to use Auth0, you would add the following dependency:
<dependency>
<groupId>com.auth0</groupId>
<artifactId>java-jwt</artifactId>
<version>3.4.1</version>
</dependency>Once you’ve added the dependency, you can configure it by setting up a security configuration file or using annotations.
4. Use A Custom Security Solution
You can always roll your security solution if you need more control over your security setup. This is generally not recommended, as it’s easy to make mistakes that could leave your application vulnerable. However, if you’re comfortable coding your security solution, this can be a viable option.
To use a custom security solution in a Spring Boot project, you’ll need to add the appropriate dependencies to your project. For example, if you wanted to use JWT for authentication, you would add the following dependency:
<dependency>
<groupId>com.auth0</groupId>
<artifactId>java-jwt</artifactId>
<version>3.4.1</version>
</dependency>Once you’ve added the dependencies, you can configure it by setting up a security configuration file or by using annotations.
Whatever option you choose, implementing Spring Boot security in the project is relatively easy. Just be sure to take the time to properly configure and test your security setup before deploying your application to production.
Advantages Of Implementing Security In Spring Boot Project

- Protects your application from unauthorized access: By adding security to your Spring Boot project, you can help protect your application from malicious users who may try to gain access to sensitive data or perform other unauthorized actions.
- Improves the overall security of your application: By adding security features to your application, you can help secure the data stored in your database and the code and configuration files used by your application.
- Meet compliance requirements: If your organization must comply with specific security standards, such as those set by the Payment Card Industry (PCI) Data Security Standard, implementing security in your Spring Boot project can help you meet those requirements.
- Improve the performance of your application: By adding security features to your application, you can help improve its overall performance by reducing the number of requests that need to be processed by your application server.
- Reduce the cost of your application: By adding Spring Boot security features to your application, you can help reduce the overall cost of your application by reducing the number of resources that need to be allocated to processing requests.
Disadvantages Of Implementing Security In Spring Boot Project
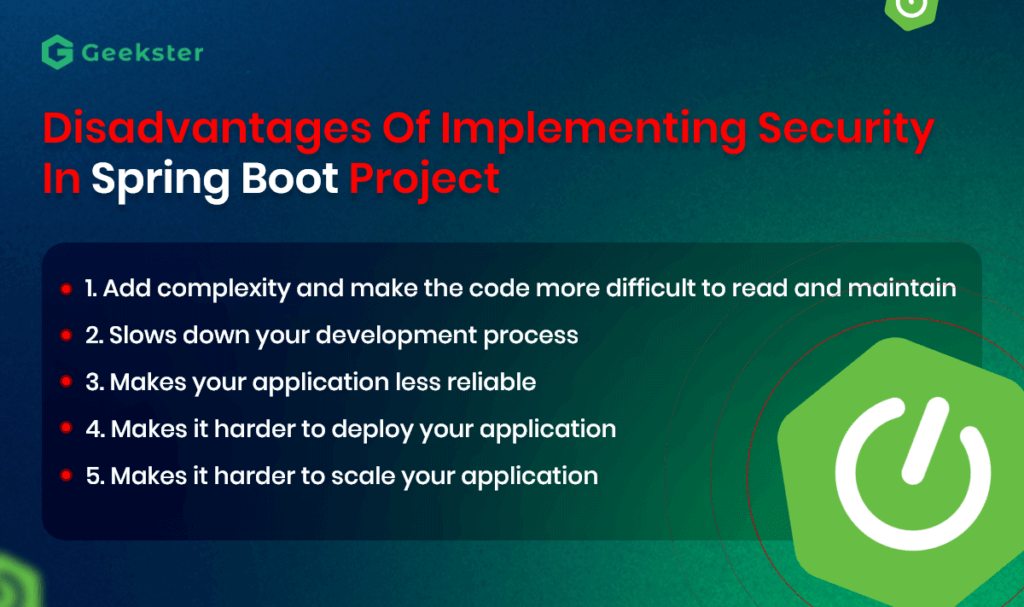
- Add complexity and make the code more difficult to read and maintain: Security features can add a lot of sophistication to your code, making it more difficult to read and understand. This can make it more difficult to find and fix bugs.
- Slows down your development process: Implementing security features can slow down your development process. This is because you have to take care of both the security aspects of your code and the functionality of your code.
- Makes your application less reliable: If security features are not implemented correctly, they can be less reliable. Chances are, security vulnerabilities can be exploited to attack your application.
- Makes it harder to deploy your application: Any missing security feature can make it harder to deploy your application. And later, you may need to configure additional security settings to deploy your application securely.
- Makes it harder to scale your application: Also, you can feel issues with scaling your application if you don’t scrutinize security features thoroughly. They can make it harder to scale your application. You may need to implement additional Spring Boot security measures to keep your application secure at scale.
Best Practices For Implementing Security In The Spring Boot Project:
- Use Spring Security: One of the best ways to add security to the Spring Boot project is to use the Spring Security framework. This framework provides a comprehensive set of features for securing your application, including authentication, authorization, and data security.
- Use HTTPS: When transmitting sensitive data, it’s important to use HTTPS instead of HTTP. This will help ensure that data is transmitted securely between your browser and the server.
- Use OAuth2 for Authentication: OAuth2 is an open standard for authentication widely used on the web. It allows users to log in using their credentials from third-party providers such as Google, Facebook, and Twitter.
- Use Authorized Access Levels: To prevent unauthorized access to your data, it’s essential to use authorized access levels. This means that only users with the appropriate permissions can access specific data.
- Use Encryption: Encrypting your data is a great way to help keep it secure. There are many different encryption algorithms that you can choose from, so be sure to select the appropriate one for your needs.
- Use a Web Application Firewall: A web application firewall (WAF) is software that helps protect your web application from attacks. It works by filtering incoming traffic and blocking malicious requests.
- Implement Security in Your Database: When storing sensitive data in a database, it’s crucial to implement Spring Boot security measures such as Encryption and authorization. This will help ensure that only authorized users can access the data.

